 In automotive cybersecurity news this week are Frost and Sullivan, FEV and HARMAN. Frost and Sullivan offer a new report, FEV analyzes the recent BMW and Audi hacks. HARMAN is offering a free cybersecurity webinar.
In automotive cybersecurity news this week are Frost and Sullivan, FEV and HARMAN. Frost and Sullivan offer a new report, FEV analyzes the recent BMW and Audi hacks. HARMAN is offering a free cybersecurity webinar.
F&S Report AV Needs Cybersecurity
The move toward connected and autonomous vehicles is reflected in the increasingly complex electronic and digital architecture of vehicles. However, while the focus has been resting on the value derived from these technologies, the risks and threats associated with them tend to be overlooked.
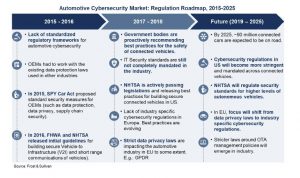 Frost & Sullivan predicts that by 2025, 80% of new vehicles sold in Europe will be connected while in the United States, this number goes up to 90%. When it comes to cybersecurity, the automotive industry
Frost & Sullivan predicts that by 2025, 80% of new vehicles sold in Europe will be connected while in the United States, this number goes up to 90%. When it comes to cybersecurity, the automotive industryhas not been quick enough to drive change and enhance their capabilities. Security developments have seemingly
been driven more by external threats, and not by roactive internal innovation.
New analysis by Frost & Sullivan, “An Insight on Cybersecurity Complexities and Initiatives in the Automotive Industry,” finds that car manufacturers are acknowledging are increasingly making automotive cybersecurity a strategic priority. Automakers are actively developing inclusive, multi-layered security solutions.
Download here.
FEV Analyzes Automotive Cyber attacks
 BMW and VW/Audi are the most recent automotive cyber victims. Fortunately the vulnerabilities were uncovered by researchers and the reports published. FEV looked at the attacks’ similarities and differences and outlined lessons automakers should learn from the hacks.
BMW and VW/Audi are the most recent automotive cyber victims. Fortunately the vulnerabilities were uncovered by researchers and the reports published. FEV looked at the attacks’ similarities and differences and outlined lessons automakers should learn from the hacks.
Computest (VW/Audi) published their research on the VW/Audi vulnerabilities and Keen Security Lab (BMW) published theirs on BMW. Although the vulnerabilities are not presented in technical detail the results from the publications are relevant to every automotive professional (not just cyber security professionals). FEV’s goal is to spark a discussion of the hacks similarities and differences so everyone can not only learn from their findings, but also take a look at their own products driving on the road every day.
The article notes that some may contend the models from Volkswagen, Audi an BMW are 2015, 2016, and 2017 therefore the vulnerabilities are outdated and irrelevant. However, the vulnerabilities highlighted by these publications are architectural and process weaknesses common throughout the automotive industry with a secondary focus on OEM specific vulnerabilities.
Both research teams started by finding models with certain features connectivity features.
Automakers should note that connectivity is the target. Attention has moved away from CAN or solely physical or component attacks to connected services in the automotive domain. Hence, focus your strengths and might more towards securing connectivity.
The primary targets are the Infotainment Unit, Telematics Unit and Central Gateway – a typical architecture for any car on the road. It is a more secure to have a central gateway segregating the in-vehicle network with the external world of connectivity. However, the BMW architecture has a Telematics Unit connected to the Infotainment Unit over USB.
Once the target vehicles were shortlisted and the target modules were identified, the researchers went through each interface. Both the publications show that the researchers performed respective analysis on cellular, Bluetooth, USB, OBD-II, and phones.
The BMW researchers identified vulnerabilities in USB (USB-to-Ethernet), Bluetooth and were able to take advantage of the cellular interface to showcase a remote hack. They also leveraged the OBD-II interface and demonstrated a physical attack scenario. Computest (VW/Audi) targeted the USB (USB-to-Ethernet), Wi-Fi and the cellular interfaces.
The Keen Security Lab (BMW) researchers presented and focused on both remote and physical attack scenarios resulting in a demonstrable attack. Computest (VW/Audi), on the other hand, focused solely on proving remote attacks by illustrating individual component vulnerabilities and, in some cases, theoretical attack scenarios.
Route to QNX
The first step the researchers did was to scan any and all available interfaces . They scanned the USB, OBD-II, and cellular interfaces to determine what was there. A USB (specifically USB-to-Ethernet) port scan using Nmap was used to identify what services were running on the vehicle. Nmap uses simple command line instructions and is available for both Windows and Linux. Not surprisingly, the researchers all reached the same destination – QNX.
With their first scans they found vulnerabilities and were able to get root access to Infotainment Units running QNX. QNX has 50% market share (as reported in 2015); 50 million vehicles have QNX running. Not included in the vehicles researched in these studies are QNX-using vehicles from GM, Mercedes-Benz, Toyota, Porsche, and Land Rover.
Once both research teams got root access to the Infotainment Units, they were able to perform local code executions.
They did not stop with USB, the went deeper through cellular connected. They reached similar attack goals by two different methods over cellular. Keen Security Lab (BMW) set up a local cellular network using Universal Software Radio Peripheral (USRP) and OpenBTS. Computest (VW/Audi) used the client-to-client communication feature and assigning public IPv4 addresses to target vehicles from an ISP.
SUBSCRIBE
You are welcome to subscribe to receive email notification of publication of Connected Car News Cybersecurity, you can also get weekly news summaries or daily emails.
Keen Security Lab (BMW) even analyzed Bluetooth and the E-NET OBD-II interfaces and found vulnerabilities in both. USB-to-Ethernet allows the end consumer to update their vehicle via a USB dongle. With more interfaces performing the same task means double the vulnerabilities.
The publications did not reveal the exact executable code that is vulnerable, but the high-level vulnerability areas to consider are root access, memory corruption and code signing. Both research teams identified code signing vulnerabilities. They are not cryptography vulnerabilities, but highlight inconsistent implementation vulnerabilities.
LESSONS LEARNED
- Connectivity is the target
- Open source open doors for hacking.
- Automakers should master only one update method.
- Automakers need to deploy security solutions consistently.
HARMAN Automotive Cybersecurity Webinar
There is afree Webinar on Cybersecurity for Connected and Autonomous Cars featuring speakers from IHS Markit and HARMAN. In this Webinar, you will learn.
- The role of Cybersecurity software and services in Connected and Autonomous Cars;
- Worldwide forecasts for Automotive Cybersecurity and projected growth for ADAS units;
- Where OEM’s stand on this critical, and potentially lifesaving practice;
- Why the time to implement Cybersecurity practices is now.
The speakers will provide their unique perspectives on the changes our industry is facing. Yuval Weisglass, Vice President, Automotive Cybersecurity, HARMAN and Colin Bird, Sr. Analyst, Automotive Software, Apps, Services, IHS Markit, will discuss how recent trends will impact cybersecurity and answer live questions from those viewing the webinar.
Date: Wednesday, June 27
Time: 8 am PST, 11 am EST, 5 pm CEST, 11pm Beijing
Register