 Researchers Sheila Ayelen Berta and Claudio Caracciolo have created a tiny back hardware backdoor for the CAN bus, called “The Bicho”. They will be presenting it on unlucky April 13 at HITBSecConf in Amsterdam that connects to the vehicle’s OBD-II port. The pair have been called “Hack in the Box Duo.”
Researchers Sheila Ayelen Berta and Claudio Caracciolo have created a tiny back hardware backdoor for the CAN bus, called “The Bicho”. They will be presenting it on unlucky April 13 at HITBSecConf in Amsterdam that connects to the vehicle’s OBD-II port. The pair have been called “Hack in the Box Duo.”
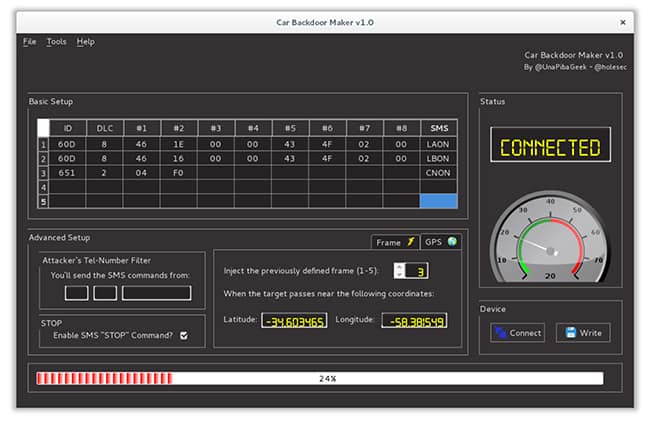
The Bicho supports multiple attack payloads and it can be used against any vehicle that supports CAN, without limitations regarding manufacturer or model. Each one of the payloads is related to a command that can be delivered via SMS, this way it allows remote execution from any geographical location. The hardware backdoor has an intuitive graphical interface, called “Car Backdoor Maker”, which is open-sourced and allows payload customization.
The break-in attached by using a SIM800L GSM module. All a hacker has to is insert the GSM chip to “know the phone numbers.”
After an SMS is sent to that telephone number, the firmware of the hardware backdoor will know what it has to do. A database called OpenCANdb shows what the different CAN frames are for different automakers. For example turning on the lights or messing with the tachometer.
The attack payload can be configured to be automatically executed once the target vehicle is proximate to a given GPS location. The execution can also be triggered by detecting the transmission of a particular CAN frame, which can be associated with any given factor, such as: the speed of the vehicle, its fuel level, and some other factors.
In the HITB talk, the pair will present a new feature, that allows users to remotely kill the car’s ECU and consequently causing the car to stop working suddenly.
The Bicho hardware device connects to the CAN bus via the vehicle’s OBD-II port.
The researchers note, “Being curious does not mean being reckless, so we strongly suggest that if you try to test these CAN frames, take all the security measures, this is especially intended for all those frames that affect the engine, the brakes or the accelerator. ”
They believe that their research and presentation is to make people and manufacturers aware of the high risk of car hacking.
See their Car Hacking Village presentation from DefCon.
https://youtu.be/fvMqIph6-Fk
SUBSCRIBE
You are welcome to subscribe to receive email notification of publication of Connected Car News Cybersecurity, you can also get weekly news summaries or daily emails.