 Kaspersky Lab tested Android apps for remote control of cars from several famous car manufacturers to see how easily they could be hacked. They found that all of the applications contain a number of security issues that could potentially allow criminals to cause significant damage for connected car owners. Kaspersky suggests Android app users keep their software up-to-date and install a security software.
Kaspersky Lab tested Android apps for remote control of cars from several famous car manufacturers to see how easily they could be hacked. They found that all of the applications contain a number of security issues that could potentially allow criminals to cause significant damage for connected car owners. Kaspersky suggests Android app users keep their software up-to-date and install a security software.
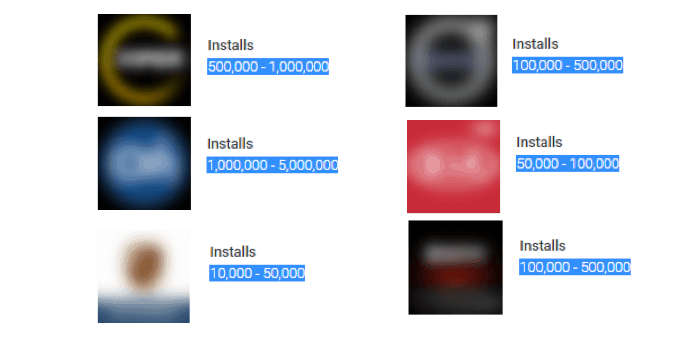
Reasearcher looked at apps that Google Play statistics show have been downloaded tens of thousands, and in some cases, up to five million times. The researchers discovered that each of the examined apps contained several security issues. Some apps can be easily decompiled, don’t check to see if Android is rooted, lack integrity in verification, user names /passwords/VIN stored in plain text, saving of debuging file on the SD card. The good news is some apps also needa pin that can only be acessed from the car itself. The apps also lacked of protection against app overlaying techniques.
Upon successful exploitation, an attacker could gain control over the car, unlock the doors, turn off the security alarm and, theoretically, steal the vehicle.
In each case the attack vector would require some additional preparations, like luring owners of applications to install specially-crafted malicious apps that would then root the device and get access to the car application. However, as Kaspersky Lab experts have concluded from research into multiple other malicious applications, which target online banking credentials and other important information, this is unlikely to be a problem for criminals knowledgeable in social engineering techniques, should they decide to hunt for owners of connected cars.
The researcher concluded that being an expensive thing, a car requires an approach to security that is no less meticulous than that of a bank account. Although it should be noted that we have not witnessed a single attack on an app that controls cars, and none of the thousands of instances of our malware detection contain a code for downloading the configuration files of such apps. However, contemporary
“Trojans are quite flexible: if one of these Trojans shows a persistent ad today (which cannot be removed by the user himself), then tomorrow it can upload a configuration file from a car app to a command-and-control server at the request of criminals. The Trojan could also delete the configuration file and override it with a modified one. As soon as all of this becomes financially viable for evildoers, new capabilities will soon arrive for even the most common mobile Trojans,” noted the report.
Kaspersky Lab researchers advise users of connected car apps to follow these measures in order to protect their cars and private data from possible cyberattacks:
- Don’t root your Android device because it this will open almost unlimited capabilities to malicious apps.
- Disable the ability to install applications from sources other than official app stores.
- Keep the OS version of your device up to date in order to reduce vulnerabilities in the software and lower the risk of attack.
- Install a proven security solution in order to protect your device from cyberattacks..
This research was presented in “Hey Android, Where’s My Car?” at the RSA Conference on February 16, 2017.